Exploits Explained: How Log4j, Buffer Overflows and Other Exploits Work
Vložit
- čas přidán 10. 07. 2024
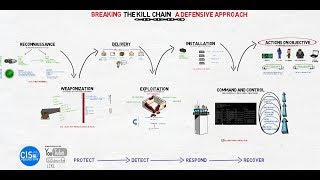
- Exploits represent any piece of code, data or sequence of commands that targets a vulnerable application for the purpose of gaining unauthorized access. Log4j is one of the most popular recent exploits that is widely considered to be the most dangerous exploit of our time.
In this video, we will break down the anatomy of an exploit, and how each part of the malicious code comes together to target a vulnerable application. We’ll discuss the three distinct parts most exploits have in common, as well as a deep dive into Log4j.
Exploit Anatomy 0:51
Lof4j Overview 1:12
Types of Exploits 2:25
Buffer Overflows 2:44
Buffer Overflow Demo 3:18
Shell Codes 4:07
Jumping the Memory Stack 5:26
Payloads 5:49
Meterpreter 6:30
Layered Defense Against Exploits 7:05 - Věda a technologie








this channel is amazing, and your explanations are incredibly clear and comprehensible
Thank you very much Igor! Happy I could help
No regrets in subscribing this Channel.
Thank you so much for sharing the knowledge.
best cybersecurity channel in youtube for sure! love the pictures and the way you explain things. Please keep it up!
Much appreciated, thank you !
Great video!
Great explanation. Great channel.
Much appreciated!
Welcome back :)
can you do like...more videos, this is one of the best resources I use for modern security practices
Last 12 months have been very busy but currently have 2 videos in progress and trying to make it a priority over the next few months. Thanks for the support!
You are awesome!
Thank you! Really appreciate your support
thanks, what software did you use to make the animated illustrations in the video?
14'th
Letsgoo🤘🏼. Size 10 @_raff_raff