IT / Information Security Risk Management With Examples
Vložit
- čas přidán 22. 06. 2024
- This lecture is the part one of series for the IT / Information Security Risk Management.
The video is good for students preparing for exams and interviews.
The video covers the following topics:
- Risk Management
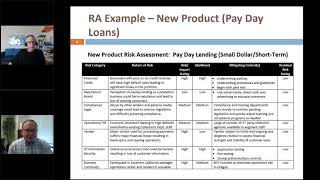
- Risk Assessment
- Risk Treatment
- Asset / Process Based Risk Assessment
- Qualitative, Quantitative and Semi Quantitative Risk Assessment / Management;
- And the definitions to understand these areas.








Watching it again and it even got better!
Excellent job!! You are great!
Thank you very much!
Thank you for your time and effort at creating this. Good job. Keep it up. I learned something new too.
Thank you very much. I really appreciate it.
One of the excellent and crisp explanations that I have seen so far. Thank You so much!
Thank you @ramganesh
Excellent content for beginners. Thank you for your effort
Thank you very much Adil.
I’m an info sec risk analyst for my bank. This is great resource!!
Thank you very much. Really appreciate it!
You put everything in order and the explanation was so comprehensive
Thank you very much for your kind feedback
I will be joining as a Information Security Risk Analyst next month. This will help me prepare. Thank you.
It definitely will. Do let me know on what other topics you would like to hear me on.
Excellent delivery. Thank you.
Thank you very much Kester. I really appreciate it.
Thank you, extremely helpful
Wow…. Great explanation and well organized. 👏👏👏
Thank you very much Asanka!
Nice initiative Ali.. 👍😇
Very easy understanding. Thanks for such working.
Thank you very much Javed! Really appreciate it.
Great information Ali. I like how you structure and explained the concepts. Keep up the good work!
Thank you very much!
good video, Thank you! but need to learn, how to implement this as well :)
Thank you and best of luck ☺️
Very concise and informative.
Thank you very much Kaleem!
Quite helpful and interesting, thank you
Thank you very much Mamta!
This is a great overview.
Thank you
It was informative, Ali! Thanks for the video
Thank you very much Ahmed. Really appreciate it.
Very good content. Thanks for sharing this
Thank you for your feedback @mayankraj2806. Really appreciate it
very good work..appreciate it
Thanks Rohit
Keep up the good work ❤️
Thank you Ziyad!
Good one.
Thank you!
Excellent Mr Ali!!
Thank you very much Ram!
Hi Ali
Would be very helpful if you can provide a link to the actual slide deck itself.
Great video! Thanks for the explanation!
👌🏻❤
Here are the learning outcomes for anyone who needs them (they're all listed at 27:59)
What is Risk?
Why do we need risk management
What is risk management?
What is risk assessment?
What is risk treatment?
What is likelihood, impact, inherent and residual risk?
Difference between threat, vulnerability and risk.
Difference between asset owner and asset custodian.
Difference between risk management and risk assessment.
Difference between quantitative, qualitative, and semi-quantitative risk management.
The Risk Management Process.
Thank you very much for this video. It came very handy. Would you be able to recommend the academic journals within IT Security Risk Assessment that I could refer to for my literature review? That will be much appreciated.
Hi Phathiswa!
Thank you for your kind words. It was encouraging.
My apologies, I am no aware about any specific academic journals within the domain. But you can always refer to standardizing bodies and international platforms like SANS for the same.
@@aliqureshi2227 so much appreciated Ali. I found something I could use by U Kumar plus the standards. Have a blessed new year 🙏
Nice !
Thanks 🙏
Great
Thank you
Are we not considering the process value/asset value for risk score calculation?
Thank you very much for bringing this up. Yes, in this video the asset valuation is not discussed in specific however, theoretically just in the context of this content, consider it be part of asset identification.
Thanks for the session , I guess in 18:01 , it should be NIST SP 800-30 in place of NIST SP 800-50 .
Thank you! and Absolutely. Apologies from my end. Will manage the rectification.
Thank you for the informative information. Do you have a default template to use?
Thanks Tausef. Unfortunately, no.
Thank you
You're welcome Jason.
An excellent way of teaching. Thanks.
In video while defining,
residual risk = inherent risk - control value
However, in overview of risk management process,
residual risk = inherent risk divided by control value
Which one is right?
Thank you very much. I would recommend to use division as it leads to a reasonable residual risk value.
Hello, i will a writing assignment about information security, security risks, security control, and the application of risk control and risk measures. So, can you help me like you make video as well as notes on it. Please help me.
What is the meaning of waiver and Derogation? in risk treatment.
Waiver and derogation are just literal jargon.
Both of them are related to risk acceptance. Waiver is where management allows you to allow a particular risk open as untreated. Same story is with derogation.
The real deal is that what constitutes such waivers and derogation? - If the risk levels are low? If risk likelihood is high but impact is low? Or the benefit realized from a particular thing is far greater in value than the impact of the risk?
If u a notes please send it
@16:45
I am sorry. Can you please translate that in to English if that is a question?
@@aliqureshi2227 Oops sorry mate i marked the timeline for my purpose
So that i can resume the video later from where i left it off
@@TVVDINAKARAN No problem! :)
انت مين
النبي عربي ياعلوه