Cryptography
Vložit
- čas přidán 16. 04. 2021
- Network Security: Cryptography
Topics discussed:
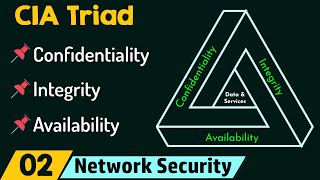
1) Introduction to cryptography and the role of cryptography in security.
2) Formal definition of cryptography and explanation with example.
3) Need for encryption and decryption in cryptography with real-world examples.
4) Importance of keys in cryptography.
5) Types of cryptography for example.
6) Symmetric cipher model and explanation.
7) Explanation of unconditionally secure and computationally secure encryption schemes.
Follow Neso Academy on Instagram: @nesoacademy (bit.ly/2XP63OE)
Contribute: www.nesoacademy.org/donate
Memberships: bit.ly/2U7YSPI
Books: www.nesoacademy.org/recommende...
Website ► www.nesoacademy.org/
Forum ► forum.nesoacademy.org/
Facebook ► goo.gl/Nt0PmB
Twitter ► / nesoacademy
Music:
Axol x Alex Skrindo - You [NCS Release]
#NetworkSecurityByNeso #Cryptography #NetworkSecurity







People are saying not repeating the same step will save viewer's time, but not everyone is as smart as you guys.... some people need different perspective to understand the concept..... grow upp guys and appreciate the creator instead of finding silly problems in this video
These lectures are amazingly helpful. Thank you so much sir 😩
Powerful lesson you've opened it up for me now i can understand this topic
Loved the explaination! Thank you.
Your All lectures are more informative
Great lecture thank you
Very well put
that's more clear than my lecture does, thanks a lot sir
Well lectures thanks for ur explanation. ❤
Thank you for the lecture
Excellent
Good explain..... Keep it up and gain users
Thanks for this video.
Very informative
Thanks a lot sir ❤️
Note : {cryptography deals with the Alot of mathematical terminology. The underlying mathematics is more important. So the keys are generated by the mathematical algorithms in order to deal with the cryptographic technique.}
informative video
best explanation
Superb
thanks a lot sir
too good!
My my bro amazing 😍
Nice bro
Starts at 0:40
Thnkyu
Sir plz complete entire course lecture.. As soon as possible.... Because sir we in 6th SEM and only watching your playlist.. Of whole video series..
How does the secret key distributed between sender and receiver.
Sir can u make videos on object oriented programming
I don't no why you not uploading data structure lectures.........
Plz sir complete this course as soon as possible.. 🙏🙏
You can also see more videos on my channel also
nice...
Thank you sir 😊
👆👆👆👆
DM me for guidance and support
thanks alot it helpful
👆👆👆👆
Dm me for guidance and support
Very helpful
👆👆👆👆👆
Dm me for guidance and support
thank
Luv u ❤
Don't have any programming based video for this explanation?
can you make video on mitre ck and att
Brain's 🧠🧠🧠 are heated
Sir/ mam it's really our pleasure to have such kind of who teaches super than our college faculty
But a graduate students we have so many topics in the syllabus ehy don't you refer B. Tech (4-1) syllabus for this subject . Please do it so make more videos on various topics which are related to student's syllabus
I hope you understand !!!
I passed my exam brother Tanq so much
👆👆👆👆
Dm me for guidance and support
Watching the day before exam🥲
Use of Problems Project Use Through the Same Problems Levels Engryption Decryption
DAMN❤❤
Key range and key size?
Please complete the DATA STRUCTURES lectures plz..
Sir said , stacks and queue are to be uploaded
@@rsingh6216 yes bro..But when ? They are saying the same to everyone. Its ok if they are not able to..cz i knw it takes a lot of time for them to do all these videos. I respect them. Just we can wait now..thats all we can do..
@@anveshatagore542 it's in my 2nd semester ,so only 3-4 months left for exam. I hope neso will upload all videos till that time.
@@rsingh6216 Hope so bro..
@@anveshatagore542 ok bro👍
Please who can guide on how to write cryptography algorithm?
Voice 🤩🤩🤩🤩🤩
😅
Very hard
No
🙏🙏🙏🙏
you mean sender uses receiver's public key to encrypt the message and that encryption is only decrypted by receiver's private key
Can I get the ppt
www.nesoacademy.org/cs/11-cryptography-and-network-security/ppts
@nesoacademy admin,
“ How RSA can defeat ‘ man in the middle attack’ you can use following scenario: Imagine a sender S wants to share a secret key K to the receiver R. What exactly the sender S has to send to the receiver R?
Unconditionally and computationally secure not clear.
Presentation was very informative and well explained, but it was too much repetitive. For ex. the first 4mins of the video.
Schedule Scheme
today is my mid sem exam😂😂🙂
Video length can be made shorter if the same topic is'nt repeated 15 times
👆👆👆👆👆
Dm me for guidance and support
I DidntKnow That.
bro why you shouting at me 🤣
Man... You need to "really" study before you start making tutorial videos. I can't imagine how many viewers have left I'll informed after learning from this video.
you could have done better 😐
too much repeated concepts, just get to the point plz
Very poor content and only repetition of content
Input 🔣🔠🔣 Output