
- 57
- 51 944
Professor Wolf
United States
Registrace 31. 01. 2024
Current content: Security + 701, How to get a Job, Introduction to Cryptography
Learn AI
Learn to build your first AI, the lines of code, concepts, and how it all comes together
github.com/VoidKnight-AI/Binary-AI
github.com/VoidKnight-AI/Binary-AI
zhlédnutí: 140
Video
1.3 Change management, technical implementations, Documentation, version control
zhlédnutí 53Před 2 měsíci
Paris Wolf teaches Security 701. Change management, technical implementations, Documentation, version control.
1.2 Physical security, Honeypot
zhlédnutí 33Před 2 měsíci
Paris Wolf teaches security 701. Physical security Bollard, fence, mantrap, sensors, Honeypot, honeynet, honeyfile
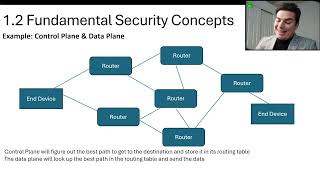
1.2 GAP Analysis, Zero Trust, Control Plane, Data Plane
zhlédnutí 106Před 2 měsíci
GAP Analysis, Zero Trust, Control Plane, Data Plane, Adaptive Identity, Threat Scope Reduction, Policy-Driven access control, Policy Administration, Policy Engine Implicit trust zones, Subject/System, Policy Enforcement Point
1.2 CIA, Non Repudiation, AAA
zhlédnutí 96Před 2 měsíci
Paris Wolf Teaches Confidentiality, Integrity, Availability, Non-Repudiation, Authentication, Authorization, Accounting
1.1 Control Types
zhlédnutí 70Před 2 měsíci
Paris Wolf Teaches Security 701. Preventative, Deterrent, Detective, Corrective, Compensating, Directive
1.0 Security Controls
zhlédnutí 103Před 2 měsíci
Paris Wolf teaches Security 701. Technical controls, Managerial Controls, Operational Controls, Physical Controls
how to get your application pulled without knowing anyone
zhlédnutí 290Před 3 měsíci
Paris Wolf teaches how to get a job by having your application pulled without knowing anyone.
Cert types ,Digital Certificate stages, states of revocation
zhlédnutí 816Před 3 měsíci
Paris Wolf teaches cryptography. Cert types ,Digital Certificate stages, states of revocation
Cryptocracking
zhlédnutí 708Před 3 měsíci
Paris Wolf teaches cryptography. Exhaustive Search, Known Plaintext attack, Man In the Middle, Chosen-Ciphertext, Active Attack, Replay attack, cut-and-paste, Time Resetting, Time attack, RSA Cracking
key escrow, anobus, AES weakness
zhlédnutí 762Před 3 měsíci
Paris Wolf teaches cryptography. key escrow, anobus, AES weakness
One, Two Way Authentication, EndtoEnd and Intermediate Authentication, Types of Authentication
zhlédnutí 764Před 3 měsíci
Paris Wolf teaches Cryptography. One/Two Way Authentication, EndtoEnd and Intermediate Authentication, Types of Authentication
CBC-MAC CCM, Windows hashing, Linux hashing
zhlédnutí 803Před 3 měsíci
Paris Wolf teaches cryptography. CBC-MAC CCM, Windows hashing, Linux hashing
PBKDF2, noncryptographic hash, Password Strength, Cloud Cracking
zhlédnutí 921Před 3 měsíci
PBKDF2, noncryptographic hash, Password Strength, Cloud Cracking
Hash collision, Preimage Attack, Birthday Attack
zhlédnutí 1,2KPřed 3 měsíci
Hash collision, Preimage Attack, Birthday Attack
Skipjack, BlowFish, TwoFish, Camilla, XTEA
zhlédnutí 1,1KPřed 3 měsíci
Skipjack, BlowFish, TwoFish, Camilla, XTEA
Entropy, Encryption, Decryption, Encoding
zhlédnutí 1KPřed 3 měsíci
Entropy, Encryption, Decryption, Encoding








I've learned more in these 4 videos than I did listening to the whole D334 book summary
Thanks Professor wolf!
Thank you for your support my liege
Thank you for sharing your knowledge
So nice of you. Consider making an i.t. Video and I will post it up!
Thank you 🙏
Any time!
Thank you 🙏
Absolutely
I liked how you explained the Get-FileHash. Thanks for that! It's one thing to learn the theory and it's another to see it in action.
glad you liked it! Feel free to make a video and I’ll post it up on the channel
Forgot to tell us to SMASH that like button, subscribe and comment if we have any questions. That is my only complaint.
Good thing I have your comment here to let everyone know!
yo professor Wolf, love this, thank you.
Thank you for your support Christian. Feel free to make a I.t. Video and I will post it!
goated professor
Thank you!
Nice intro.
You are my number one fan! My favorite fan!
Is the key to the pig pen Biometric
No it is from the 18th century
Thanks Professor Wolf
You're welcome! keep up the studies and you will be the greatest
Thanks Professor Wolf
You're welcome! keep learning so you can teach me one day!
Thanks Professor Wolf
Any time
Thanks Professor Wolf
You're welcome! If you have any more questions or need further assistance, feel free to ask. I'm here to help!
I wouldn't mind a short video on the pig pen demonstrated. Thank you for your videos!
I am very behind on projects, but can put this in the list... OR you can make it!? and I will post it up on the channel so everyone can send their valentines day sweetheart a encrypted message using Pig Pen!
Hi this video told me to comment so ya but it was a good video 🎉
@@clipper168 you should make a video and ill post it on the channel, and then they can go to your channel
Why wouldn't "TwoFish" be a correct answer to Question 42? 128 bit block, 128/192/256 key
TwoFish has a scaling key size that can range from 1 to 256 bits. Commonly used key sizes for twofish is 128/192/256. AES only has the options of 128/192/256.
Professor Wolf, This video series was very useful. I watched all the cohort videos before this series and I barely failed the PA. (40/60). I sat down and watched this whole playlist, made flashcards and notes of all the bold text. I did better on the PA the second time around and I passed the exam on the first try (all in the same day). I am not saying the cohort videos didn't help, but I wish I had watched your series first. I liked your style of instruction, and I felt like I learned more. I hope to have you as a future professor in my upcoming classes. For students starting intro to cryptography, best of luck! I definitely suggest watching all these videos in the playlist, and reviewing the material in the course chatter!
Hi thank you for the wonderful compliment @AlFromPalletTown be sure to add me on linkedin. I hope to assist everyone with positions/jobs in the future wherever that may be.
Thanks Professor Wolf!
My pleasure!
Thanks Professor Wolf!
thank you for being a wonderful student and learning all the information!
Thanks Professor Wolf!
You are the real hero! keep up the good work!
Thanks Professor Wolf!
Been very busy working on many projects! just noticed your thanks! thank you for your support
Thanks Professor Wolf
It was a honor to work with you!
Thanks Professor Wolf?
Thats me! be sure to add me on linkedin
RC DN
whats that!? RC DN?
This is great. Love the series, broken down in an easy to consume format. Thanks!
Glad you enjoyed it!
This has helped out a lot the text and others confused me
Let me know if you have any questions on any other areas. I will be posting some recruiter’s eventually so everyone can get interviews and potentially their first job
please explain pre image attack in a different if possible
Please set up an appointment with me and we can go over the topic. I will make an additional video to explain in a different way. Just very busy working on a 60m+ project for my company
Hey Professor! Is there a place to download the slides, I am a WGU student. Thank you for the videos!
Please send me a email and I can email any particular one to you. The cryptography PowerPoint has all the information, condensed
So glad you are starting a Sec+ series. Thanks Prof Wolf!!
Can it be hiring managers and ceo's in general? Not just tech related companies?
Yes, this works in any industry. If they deny you and then you build up skills sometimes they still won’t have a spot for you. Ask for a referral then and keep them updated (treat them as a mentor)
@@Professorial_Wolf what I meant was that technical roles exists in companies that do not sell technical services. Is it ideal to contact an administrator to become a programmer, or I would have a significantly stronger chance of getting a job if I contacted someone who actually does technical things.
@@johnny5941 The Non-management is less likely to assist you. Focus on management/ higher leadership within the department and the recruiters. If you reach out to a person working a admin or programing role say " I am interested in learning more about the roles within your department can you point me in the direction of the manager?" send me a request on linkedin and we can set up a call and I can give you some coaching on your personal situation. www.linkedin.com/in/paris-wolf/ the cost is be sure to subscribe!
Outstanding info, thank you so much.
Glad it was helpful! Stay tuned as I will be posting many more techniques and setting up qualified candidates with top tier recruiters
So how exactly does it work when an exchange of a fraction of a bitcoin takes place?
In addition to the block reward, miners also receive transaction fees associated with the transactions included in the block they mined. When users send Bitcoin transactions, they have the option to include a transaction fee, which is paid to the miner who successfully mines the block containing their transaction. Transaction fees are typically voluntary, but users may choose to include them to incentivize miners to prioritize their transactions.
Hey Paris, would recommend that you increase the volume of the recording a bit. I'm on full volume and I can hear you, but if I'm not in a silent environment I lose your voice.
Roger I will buy a professional mic, and redo the pre-assessments after completing each chapter
I got a Mic for all the videos moving forward now
I have never understood this type of attack before your explanation. Thanks Professor!!
Most definitely!
This clarifies so much, thank you!!
You're so welcome!
Great vid!
only the best!
Keep these gems coming! The shorter format helps me focus
I do my best to get straight to the point
Quick and to the point, thanks Professor!
AND all encompassing!
Thank you for this!! I couldn’t find any solid coverage on this topic until now. Keep up the great work!!
Glad it was helpful! This is an area most students have found difficult
Regina thomas ❤😂🎉😢😮😅😊
Awesome! these videos bring a wave of emotions. ^
Very good coverage of this topic, thank you!
Glad you liked it! Let me know if you want any specific topics covered or to go deeper into any particular subject